RESOURCES
Blog
See what's new at ID TECH
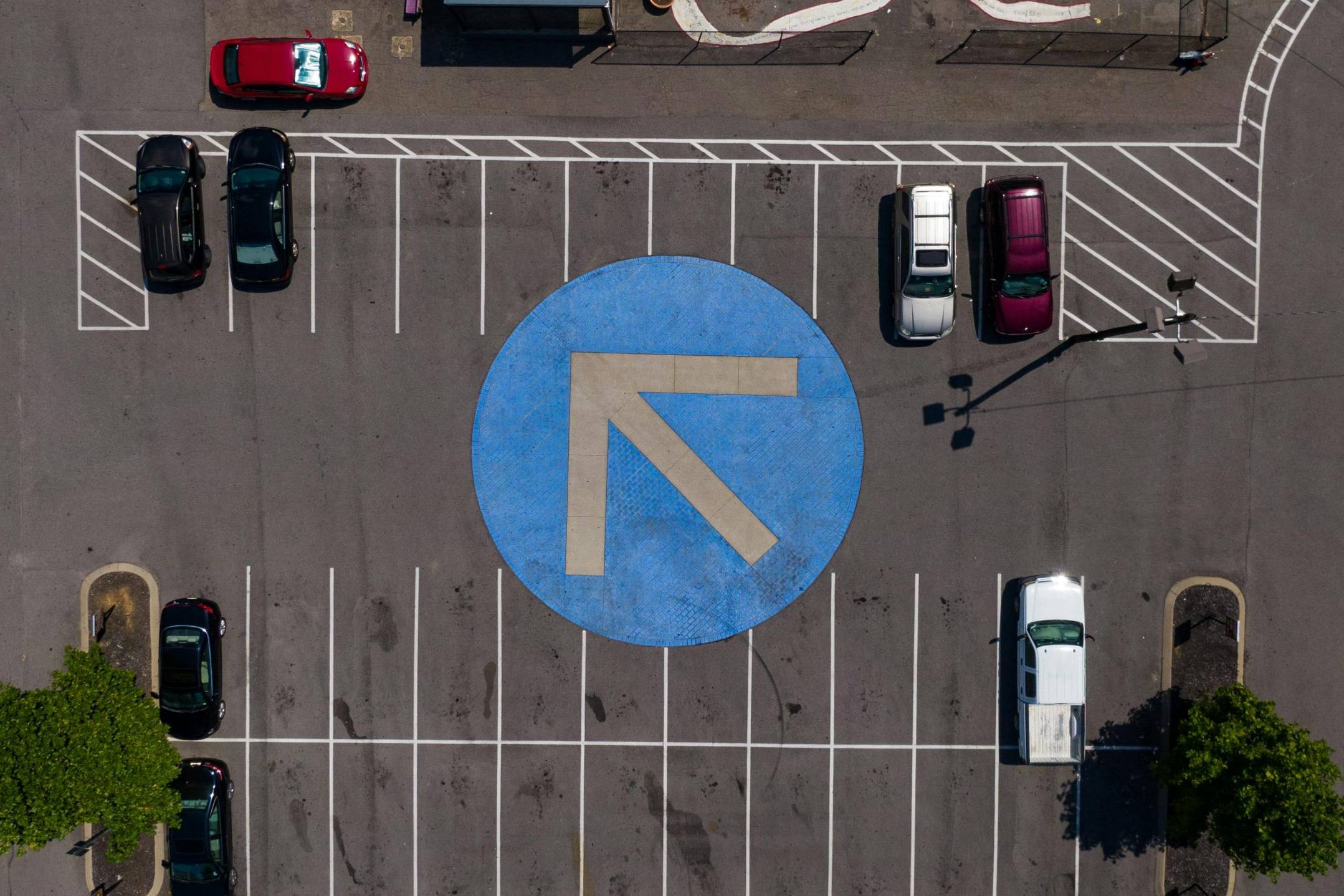
Kiosk V: The Ideal NFC Payment Reader for Parking Facilities
The Kiosk V NFC payment reader is designed to meet the demands of parking environments, making it the perfect choice for parking meters,…
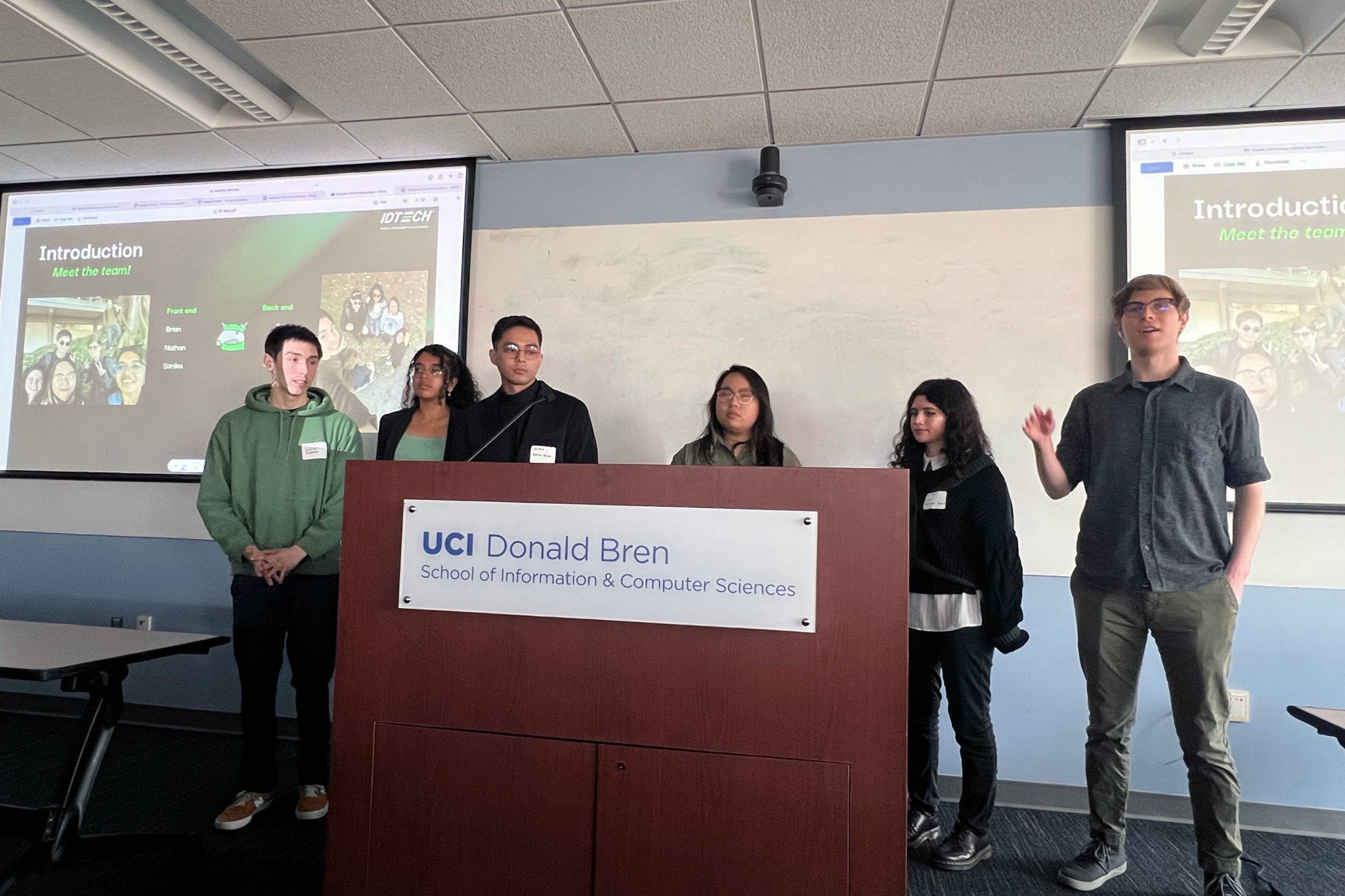
Educating Through Innovation: ID TECH’s Capstone Journey with Students at UCI
ID TECH collaborates with students at UCI's Donald Bren School of Information & Computer Sciences for a Capstone project.
ID TECH Shines at T2 Connect Conference 2024
ID TECH and T2 redefine parking payments with innovative solutions showcased at T2 Connect 2024.
VP3350 Now Ready for the Australian market with eftpos Certification
Our VP3350 mobile payment reader has achieved eftpos payment certification, making it fully compliant for deployment in the Australian…
The Evolution of Payments in the Parking Industry
The Parking industry has grown significantly over the last few years, driven by the rapid rise in population, increased vehicle ownership,…
7 Features Parking Businesses Should Consider When Shopping for Payment Solutions
In today’s fast-paced world, convenience is vital. And nowhere is this more apparent than in the parking industry. Whether it’s a bustling…
Innovate, Connect, Inspire: Our Story at the NAMA Show 2024
The bustling city of Dallas served as the backdrop for an exhilarating showcase of the latest technology and innovation in the convenience…
Revolutionizing Vehicle Commerce: Insights from EV Charging Summit & Expo
Welcome to the forefront of innovation in vehicle commerce! At ID TECH, we are committed to pushing the boundaries of what’s possible in…
7 Key Features to Look for When Shopping Mobile Payment Devices
Mobile payment readers have revolutionized the way businesses of all sizes accept payments. For small brick-and-mortar stores, food truck…
Payroc/ID TECH Partnership Simplifies Unattended Payments
Developing payment solutions for unattended parking might be one of the most demanding challenges an ISV can face. These solutions must be…
TRUSTECH 2022 – What a Difference a Year Makes!
After having missed TRUSTECH in 2021, ID TECH couldn’t pass up on the opportunity to exhibit at and attend one of the biggest shows in…
Four Things You Need to Know About Mobile Card Readers
Today’s competitive landscape demands new innovations to ensure long-term customer loyalty and satisfaction. While your current payment…
RetailNow 2022: The Following Act
RSPA is a 60-year-old organization that was initially dedicated to the point-of-sale industry with membership exclusively made up of POS…
ETA: The New and the Renewal
After a two-year hiatus filled with cancellations and virtual shows, ID TECH is happy to see in-person tradeshows have made a roaring…
ID TECH to Attend NAMA 2022
Our ID TECH team is excited to still be On the Road and attending in-person tradeshows. We can’t wait to meet our customers and colleagues…
VP3600: For All Your Banking Needs
The banking industry and technology have always been closely linked, each facilitating and encouraging advances in the other. However, in…
ID TECH is on the Road Again!
Our ID TECH team is excited to be back on the road and attending in-person tradeshows again. After a year of virtual events, we can’t wait…
Parking Payment Devices: 4 Questions to Ask
Parking payment devices have come a long way, especially in the last few years as unattended and contactless payment trends have…
ID TECH’s VP8800: Helping Marriott Offer Contactless Convenience and a ‘Commitment to Clean’
The Marriott is deploying ID TECH’s VP8800, a countertop solution that accepts all popular payment and loyalty transactions, into their…
The Rise of Artificial Intelligence in the POS World
You may have watched a movie at some point in your life where the concept of artificial intelligence (AI) captured your attention and left…
ID TECH’s VP8300 Now Supported by Cardknox
Perfect for retail merchants, the ID TECH VP8300 solution offers the fastest track to EMV-ready payment processing. With the addition of…
Exploring the Evolution of Payment Solutions
When we hover our phone or smartwatch over a payment system at our local grocery store, vending machine, parking terminal, or other retail…
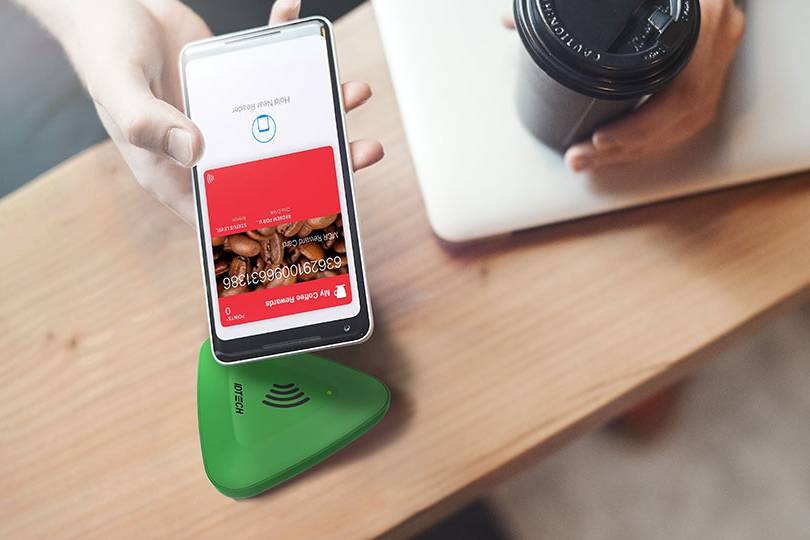
Loyalty Trends in the Mobile Industry
Digital loyalty programs are becoming an increasingly popular way for businesses to connect with their customers and gain market share. But…
Loyalty Trends in the Transit Industry
In our latest blog series, we explored payment trends within the mobile and vending industries, and learned what companies are doing to…
Loyalty Trends in the Vending Industry
As part of our latest blog series, we’re taking a look at loyalty solutions in various industries to see what companies are doing to…
Payment Trends in the Transportation Industry
In our previous article, we discussed Payment Trends in the Mobile Industry and how they have been rapidly adopted and integrated in stores…
Payment Trends in the Mobile Industry
In our previous article, we discussed Payment Trends in the Vending Industry and the technological advancements that have resulted from the…
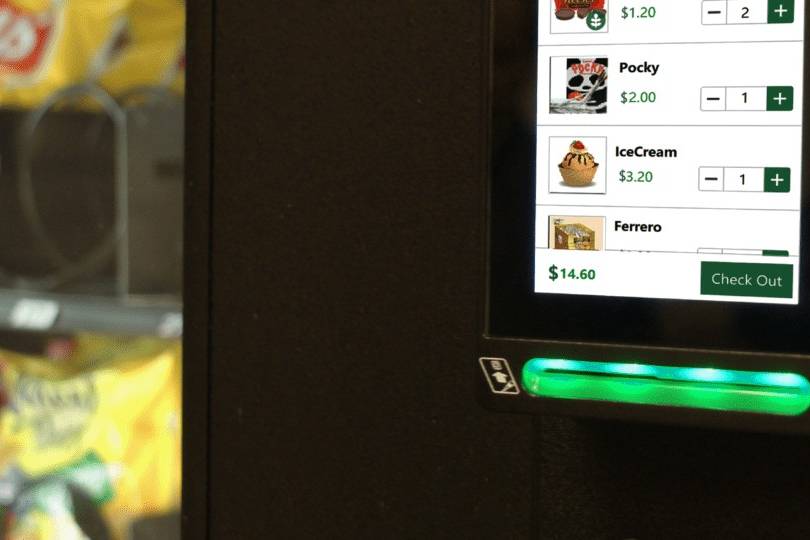
Payment Trends in the Vending Industry
From technological advancements to changes in consumer behavior, there are quite a few payment trends set to impact the vending industry…
How COVID-19 is Impacting Payments in the Transit Payments Industry
In the last few weeks, we have discussed how COVID-19 is impacting payments in the vending and mobile payments industries. Now, we will…
How COVID-19 is Impacting Payments in the Mobile Payments Industry
Last week we discussed how COVID-19 is impacting payments in the vending industry. Today we will look at how the global pandemic has…
How COVID-19 is Impacting Payments in the Vending Industry
Since the arrival of the novel coronavirus, or COVID-19, the vending industry has experience multiple changes and setbacks. There have been…
Latin America Transit Adopts EMV Contactless Payments Amid COVID-19 Pandemic
Contactless payment methods have gradually increased in popularity across the world, but COVID-19 has propelled many countries and…
What is PCI?
PCI is the association that sets security standards and regulations for the Payment Card Industry and the PCI 3.x April 30th, 2021 deadline…
EMV Certification Process in 3 Easy Steps
You may have heard of EMV (Europay, MasterCard and Visa) certification as it pertains to businesses becoming EMV compliant with the…
Contactless Payment Technology: 5 Things You Need to Know
If you use or accept credit cards, chances are you’ve heard of contactless payments. You might even use contactless payment forms such as…
What is POS Hardware?
POS hardware is the physical equipment used to process a transaction at the point of sale. You can think of it as the “point” where the…
Why “Pay and Go” Kiosks are the Future of Payments
Each month, bills come around. There’s no avoiding them, and there’s no stopping them. Although many companies are opening their payment…
Do Self Service Kiosks Actually Save Time?
These days, it seems that people will do anything to save a bit of time. Businesses and banks have been responding accordingly, offering…
Vending Machine Card Readers: 4 Things to Know
If you’re an on-the-go person and don’t like waiting in lines for snacks or drinks, or if you’re at work and need a mid-afternoon caffeine…
Tap and Go: What It Is and Why It Matters
Payments today give consumers a range of possible payment methods. Gone are the days of just cash or credit. Now, you can buy your daily…
How Payment Terminals Work
You’ve probably seen signs that say ‘payment kiosk here’ or ‘we accept Apple Pay’ in any number of stores you’ve been in recently. You’re…
EMV Chip Technology: 6 Things You Didn’t Know
You might feel like every time you walk into a store there is a different type of credit card terminal you’re swiping or dipping your card…
Fast Food Kiosks: Their Impact in 2019
Think about the last time you walked into a McDonald’s or Panera Bread. Did you order through a cashier, or did you opt to skip the line…
Chip Card Readers in 2019: Everything You Need to Know
By now, you’re used to the magnetic stripe on the back of your credit cards. You might even still use it from time to time. However, the…
Point of Sale Hardware in 2019: 5 Big Developments
With the rise of digital payments and increasing use of credit cards, merchants must keep up with payment trends. When customers sense that…
Digital Loyalty Programs: How ID TECH is Elevating the Tap-and-Go Experience
Today, brands are built around customer retention and brand recognition. Digital Loyalty programs are part of the brand experience and the…
PIN on Glass: 4 Secret Things You Need to Know
Businesses have more options for points of sale than ever before. Because of this, it is important to understand which payment types will…
EMV Compliance: What You Need to Know
EMV® technology was developed and managed by American Express, Discover, JCB, Mastercard, UnionPay, and Visa. It is a global standard for…
Payment Kiosks in 2019
Today, individuals by using a self-service interactive payment kiosk can take full control of their payments. Touch payments are one of the…
The Future of Payment Technology
Payment Technology is always evolving with its goal to make transactions as seamless and as easy as possible for good customer experience.
Moving Past Magnetic Stripe Card Readers in 2019
A magnetic stripe card is inexpensive compared to other card technologies and not hard to program. While a magnetic stripe is more…
12 Ways to Protect Your Payment Information
When you are shopping, the last thing you want to worry about is someone hacking your payment information. Whether you are buying clothes,…
13 Benefits of Restaurant Point of Sale Systems
A Restaurant Point of Sale system is typically where a customer makes a payment in exchange for goods or services. It is a combination of…
What is an EMV Card Reader?
EMV Card Readers have revolutionized the payment industry. Come learn what they are and about the impact that they have.
The Efficiency of Mobile Payments
Mobile payments are defined as transfers of funds using mobile telecommunications networks or diverse mobile devices in both the initiation…